- Home
- Redefining SOC Affordability
- Our As-a-Service Platforms
SIEM Based 24×7 SOC Monitoring
Mobile Device Management-as-a-Service
Patch Management Services
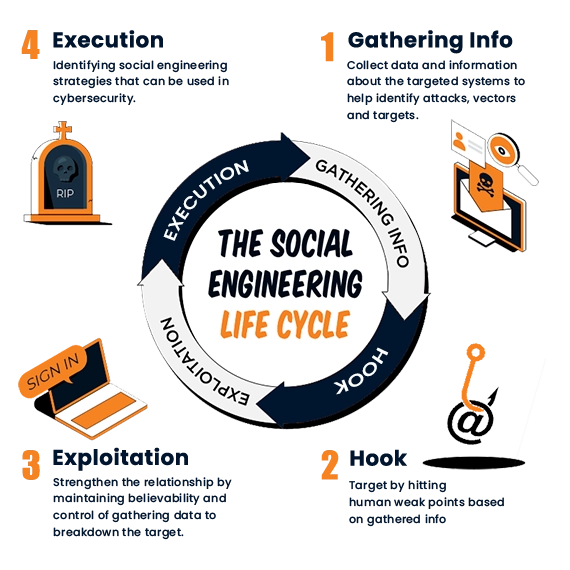
Phishing Campaign & Security Awareness Training
Xpertize Solutions
Awareness TrainingManaged Endpoint Detection & Response
Vulnerability Assessment-as-a-Service
SafeAeon Expertise-as-a-Service
Digital Forensics and Incident Response (DF/IR)
Comprehensive Incident Response Services
Managed Extended Detection and Response
Dark Web Monitoring
Dark WebMonitoring-as-a-service
Xpertize Solutions Email Security-as-a-Service
Cloud Infrastructure Monitoring
Multi-Factor Authentication-as-a-Service
Internal, External, Web App Pen Testing Services
SASE-as-a-Service
Xpertize Solutions Secure Access Service EdgeFirewall Management & Monitoring Service
- MSP Partner
- Datasheets
- Contact Us